A profession in cybersecurity entails safeguarding digital systems and data against cyber threats, presenting significant demand, robust job security, and attractive remuneration, frequently with six-figure potential. Essential positions encompass Security Analyst, Penetration Tester, Incident Responder, and Cloud Security Specialist, necessitating expertise in network security, threat detection, and artificial intelligence techniques.
GLOBAL THREAT MONITOR
REAL-TIME CYBER DEFENSE NETWORK
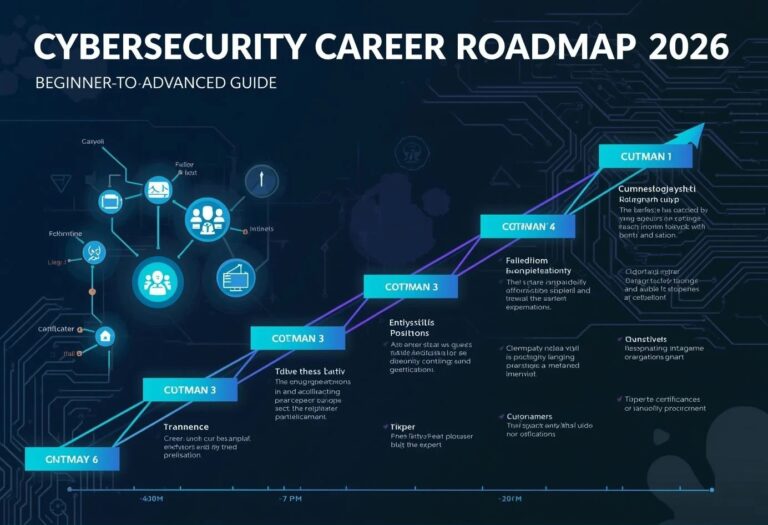
Cybersecurity Career Roadmap: Beginner to Advanced
A cybersecurity career path began with a foundation of essential IT competencies (networking, Linux, Windows), subsequently advancing to the study of security principles, securing entry-level certifications such as CompTIA Security+, and acquiring hands-on experience through home laboratories and Capture The Flag (CTF) competitions. Specialization in professions such as SOC analyst or penetration tester facilitates advancement to senior positions like Architect or CISO.

Phase 1: Foundations (Months 0-3)
- Networking Fundamentals: Understanding TCP/IP, DNS, DHCP, subnetting, and VLANs.
- Operating Systems: Acquire proficiency in Windows administration and familiarize yourself with fundamental Linux command-line operations.
- Fundamentals: Acquire proficiency in Windows administration and familiarize yourself with fundamental Linux command-line operations.
Phase 2: Beginner Certifications & Lab Work (Months 3-6)
- Certifications: Aim for CompTIA Security+ or Google Cybersecurity Certificate.
- Practical Experience: Set up a home lab using VirtualBox or VMware.
- Practice Platforms: Start with TryHackMe (beginner rooms) and PicoCTF.
Phase 3: Entry-Level Roles (Months 6-12)
- Target Roles: SOC Analyst Tier 1, IT Support Technician, Junior Security Analyst.
- Build a Portfolio: Catalog projects (e.g., firewall configuration, vulnerability assessments) on GitHub.
- Networking: Engage in LinkedIn groups, visit local Meetups, and participate in Capture the Flag competitions.
Phase 4: Specialization & Intermediate Roles (1-3 Years)
- Choose a Path:
- Blue Team (Defensive): Security Operations Center Analyst, Incident Response Specialist, Threat Intelligence Analyst.
- Red Team (Offensive): Penetration Tester, Ethical Hacker.
- Governance & Compliance: GRC Analyst, Auditor (NIST CSF, ISO 27001).
- Intermediate Certs: CySA+, PenTest+, BTL1, eJPT.
Phase 5: Advanced & Senior Roles (3+ Years)
- Senior Roles: Senior Security Analyst, Lead Penetration Tester.
- Architecture/Management: Security Architect, Security Manager, CISO (Chief Information Security Officer).
- Top Certifications: CISSP, CISM, OSCP.
Essential Tips
Continuous Learning: The threat landscape evolves rapidly; therefore, stay informed with Infosec news, research papers, and continue practicing on Hack The Box.
Practice is Key: Employers prioritize practical experience and laboratory work over mere credentials.
Document Everything: Exhibit your projects and competencies in a portfolio.
Cybersecurity is among the most rapidly expanding and lucrative sectors within the technology industry. In response to escalating cyber dangers, corporations globally are making substantial investments in security specialists. This roadmap will provide a step-by-step guidance for initiating and advancing a career in cybersecurity.
📌 Why Choose Cybersecurity in 2026?
Selecting a profession in cybersecurity in 2026 is a strategic decision, given the projected 4.5 million global job vacancies, substantial compensation potential, and heightened demand fueled by AI-driven threats and cloud integration. It presents a sustainable, dynamic career with varied roles—from ethical hacking to AI security—enabling experts to safeguard digital infrastructure against advancing cyber threats.
- Massive Talent Shortage & Job Security: The demand for cybersecurity professionals exceeds the available workforce, resulting in a global deficit of such experts, with around 750,000 vacancies in the U.S. alone, thereby guaranteeing substantial job security and swift career progression.
- High Earning Potential: The severe deficit of trained labor in cybersecurity results in pay that above market averages, coupled with considerable growth potential as experts obtain certifications.
- AI-Driven Landscape: In 2026, the domain is characterized by AI-driven threats and responses, resulting in a significant demand for experts adept in both AI and security.
- Diverse and Evolving Roles: Opportunities exist for varied skill sets, including Cloud Security Engineers, AI Security Specialists, Incident Response Specialists, and Risk, Governance & Compliance (GRC) Analysts.
- Continuous Learning and Impact: The field is dynamic, demanding continual adoption of new technologies, hence creating a difficult and fulfilling atmosphere in which specialists actively safeguard digital trust and infrastructure.
🧭 Cybersecurity Career Roadmap Overview
- Beginner Level (0–6 months)
- Intermediate Level (6–18 months)
- Advanced Level (18+ months)
🟢 1. Beginner Level (0–6 Months)
🎯 Goal:
Build foundational knowledge in IT and security basics.
📚 Learn the Basics
Start with fundamental IT concepts:
- Networking basics (IP, DNS, TCP/IP)
- Operating systems (Linux & Windows)
- Basic programming (Python recommended)
- Computer hardware fundamentals
🔧 Essential Skills
- Command line usage (Linux terminal)
- Basic networking tools (ping, traceroute)
- Understanding of cybersecurity concepts (CIA triad)
🧪 Tools to Learn
- Wireshark (network analysis)
- Nmap (network scanning)
- VirtualBox (lab setup)
📜 Beginner Certifications
- CompTIA IT Fundamentals (ITF+)
- CompTIA Network+
- CompTIA Security+
💼 Entry-Level Roles
- IT Support Technician
- Junior Security Analyst
- Help Desk Technician
🟡 2. Intermediate Level (6–18 Months)
🎯 Goal:
Gain hands-on experience and specialize.
🔐 Choose a Career Path
You can specialize in:
1. Ethical Hacking / Penetration Testing
- Learn vulnerability scanning
- Practice on platforms like TryHackMe & Hack The Box
2. Security Operations (SOC Analyst)
- Monitor threats
- Learn SIEM tools
3. Network Security
- Firewalls and IDS/IPS
- Secure network architecture
4. Cloud Security
- AWS / Azure security basics
🧪 Tools to Master
- Metasploit
- Burp Suite
- Splunk
- Nessus
📜 Intermediate Certifications
- CEH (Certified Ethical Hacker)
- CompTIA CySA+
- eJPT (eLearnSecurity Junior Penetration Tester)
💼 Job Roles
- SOC Analyst (Tier 1/2)
- Penetration Tester (Junior)
- Security Analyst
🔴 3. Advanced Level (18+ Months)
🎯 Goal:
Become an expert and specialize deeply.
🔐 Advanced Skills
- Threat hunting
- Malware analysis
- Reverse engineering
- Cloud security architecture
- Incident response
🧪 Advanced Tools
- CrowdStrike
- Palo Alto Firewall
- Elastic Stack
- Cobalt Strike
📜 Advanced Certifications
- CISSP (Certified Information Systems Security Professional)
- OSCP (Offensive Security Certified Professional)
- CISM (Certified Information Security Manager)
💼 High-Level Roles
- Security Engineer
- Cybersecurity Consultant
- Threat Intelligence Analyst
- Chief Information Security Officer (CISO)
A cybersecurity career trajectory entails understanding IT principles (networking, Linux), acquiring certifications such as CompTIA Security+, obtaining practical experience through laboratories and Capture The Flag (CTF) events, and specializing in domains like cloud security or ethical hacking. The career trajectory advances from entry-level positions (SOC Analyst) to mid-level roles (Engineer) and ultimately to executive positions (CISO).
Phase 1: Foundation (IT Basics)
Before diving into security, you must understand how systems work.
- Networking Basics: TCP/IP, DNS, Firewalls.
- Operating Systems: Proficiency in Linux and Windows.
- Fundamental Skills: Fundamental comprehension of security principles (encryption, malware, threats).
Phase 2: Entry-Level & Certifications
- Certifications: CompTIA Security+ is strongly advised as an initial certification. Other entry options include Cisco Certified Support Technician (CCST) Cybersecurity.
- Initial Roles: IT Support, System Administrator, or entry-level IT positions (6-8 months).
- Practical Experience: Establish a home laboratory, participate in Try Hack Me or Hack The Box, and compete in Capture The Flag (CTF) competitions.
Phase 3: Specialized Mid-Level Roles
Upon establishing core knowledge, progress into specialized positions:
- SOC Analyst (Blue Team): Monitoring and defending systems.

- Penetration Tester/Ethical Hacker (Red Team): Evaluating defenses through the simulation of assaults.
- Incident Responder: Mitigating breaches.
- Threat Intelligence Analyst: Tracking adversarial techniques.
Phase 4: Advanced & Specialized Career Growth
- Advanced Certifications: CISSP, CISM, or specialized certifications in digital forensics or cloud security.
- Specialized Roles: Security Architect, Security Consultant, or Chief Information Security Officer (CISO).
Continuous Learning
The threat landscape is ever evolving, demanding continuous education, the acquisition of new certifications, and the enhancement of technical capabilities in AI and cloud security.
💰 Cybersecurity Salary Overview
| Level | Salary Range (Global Avg) |
| Beginner | $40,000 – $70,000 |
| Intermediate | $70,000 – $120,000 |
| Advanced | $120,000+ |
🧠 Key Skills You Must Develop
- Problem-solving mindset
- Analytical thinking
- Attention to detail
- Continuous learning
🛠️ Build Your Cybersecurity Lab
Create your own practice environment:
- Install Kali Linux
- Use Virtual Machines
- Practice hacking legally
- Join bug bounty programs
🌐 Best Platforms to Learn Cybersecurity
- Coursera
- TryHackMe
- Hack The Box
- Cybrary
- Udemy
🚀 Pro Tips to Succeed Faster
Prioritize "deep work" on your most impactful activity for 90 minutes each morning, apply the 1% rule to achieve incremental daily enhancements, and proactively delegate or eliminate non-essential chores. Success is expedited by ceasing multitasking, pursuing mentorship to accelerate your learning curve, and adopting a "no Plan B" mindset to ensure unwavering growth.
Strategic Execution
- The 90-90-1 Rule: For the subsequent 90 days, dedicate the initial 90 minutes of your day to your foremost priority. This guarantees that your optimal energy is directed towards tasks that significantly impact progress.
- Leverage Mentorship: Do not replicate existing solutions. Identify an individual who has achieved your desired goals and gain insights from their experiences, errors, and methodologies.
- Aggressive Simplification: Most duties comprise just busywork. Systematically eradicate, automate, or subcontract any task that does not directly advance your primary objective.
- The 1% Rule: Rather than pursuing "overnight" achievement, strive for a daily enhancement of merely 1%. Accumulated over the course of a year, these incremental advances yield exponential growth.
Mindset & Focus
- Define Your "Why": In the absence of a unique, individualized definition of success, you will waste time pursuing the objectives of others. Document it to maintain your grounding.
- Stop Multitasking: It is detrimental to productivity. Concentrate on completing one project prior to commencing the subsequent one.
- Reframe Failure: Regard setbacks as critical data points. If you do not experience occasional failure, you are not undertaking enough significant risks.
- Limit Negative Influences: Success at a rapid pace is unattainable if you are bound to others or surroundings that deplete your energy.
Tactical Habits
- Plan the Night Before: Never start your day deciding what to do. Write your to-do list the night before so you can hit the ground running.
- Eat the Frog: Tackle your most challenging or anxiety-inducing task first. Once it is done, the rest of the day becomes easier.
- Learn Constantly: Whether through books, courses, or podcasts, dedicate time to expanding your knowledge base daily.
- Protect Your Health: You cannot sustain "fast" growth if you burn out. Prioritize sleep, nutrition, and exercise as professional requirements, not luxuries.
CyberSec Career Vault
🔑 Final Thoughts
Cybersecurity is not just a profession; it is a maintaining adventure of perpetual education. This roadmap will assist both novices without an IT background and individuals transitioning jobs in establishing a robust foundation and advancing to expertise. Commence modestly, maintain consistency, and persist in practice.
👉 Start your cybersecurity journey today and secure your future!

2 thoughts on “Cybersecurity Career Roadmap 2026: Beginner to Advanced Guide”